A few days ago, when I made the decision to build my digital portfolio, I promptly purchased two servers with public IPs, directly accessible over the internet. Given my background is primarily in infrastructure and automation solutions, I initially overlooked the critical need for robust security measures to protect my servers right from the start. However, last night, I noticed a significant slowdown in one of my servers, which led me to suspect it was under attack to some degree.
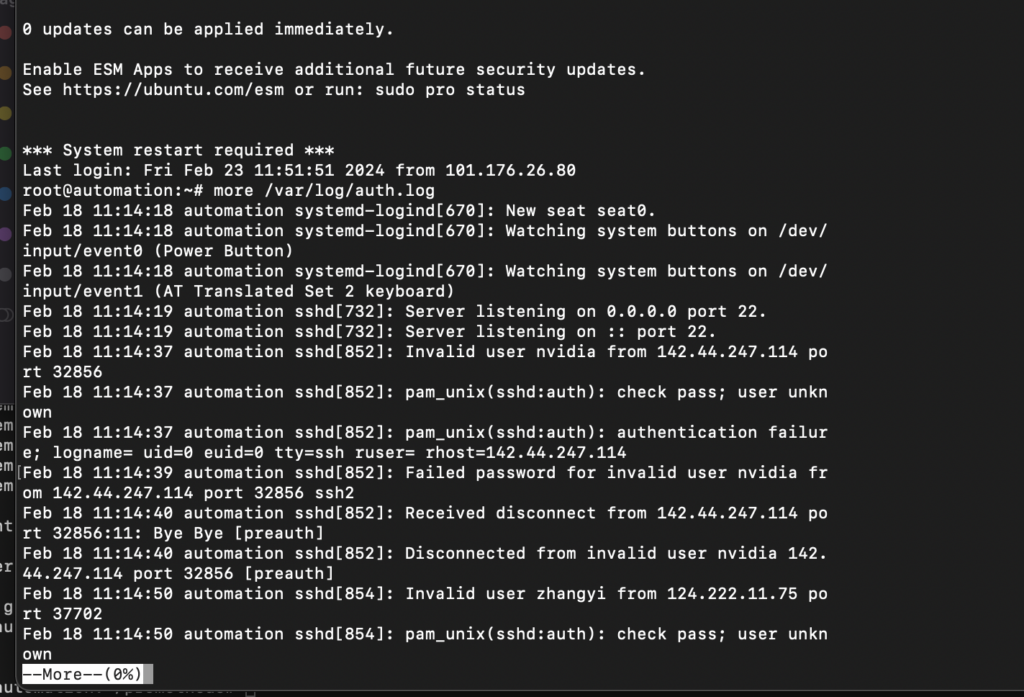
Upon investigating the server and reviewing the SSH authentication logs, I discovered that, from the moment my server went live, it had been bombarded with millions of brute-force attack attempts.
After examining the logs, I recognized the necessity to deactivate password-based SSH access and switch to utilizing RSA keys for authentication.
Consequently, I used the command "ssh-keygen -t rsa -b 4096" to create SSH key pairs on my local machine. Afterward, I transferred the public key to my two servers using the command "ssh-copy-id -i ~/.ssh/<public_key>.pub <user>@<server_ip>".
For ease of access when connecting to my servers, I established aliases in my local .zshrc file for the connection commands to each server.
Following the alias configuration, I proceeded to log into the servers to turn off the password authentication feature of the sshd daemon. This was achieved by appending the configuration line “PasswordAuthentication no” to the sshd_config file. Subsequently, I executed the command systemctl restart sshd to apply and activate the changes.
To restrict the number of SSH connection attempts, specifically blocking further attempts after more than three failed requests, I installed SSHGuard using the command sudo apt install sshguard.
Following the implementation of security measures, I revisited the SSH access logs and observed numerous failed connection attempts, along with blocking entries from SSHGuard. Below are the screenshot for reference.
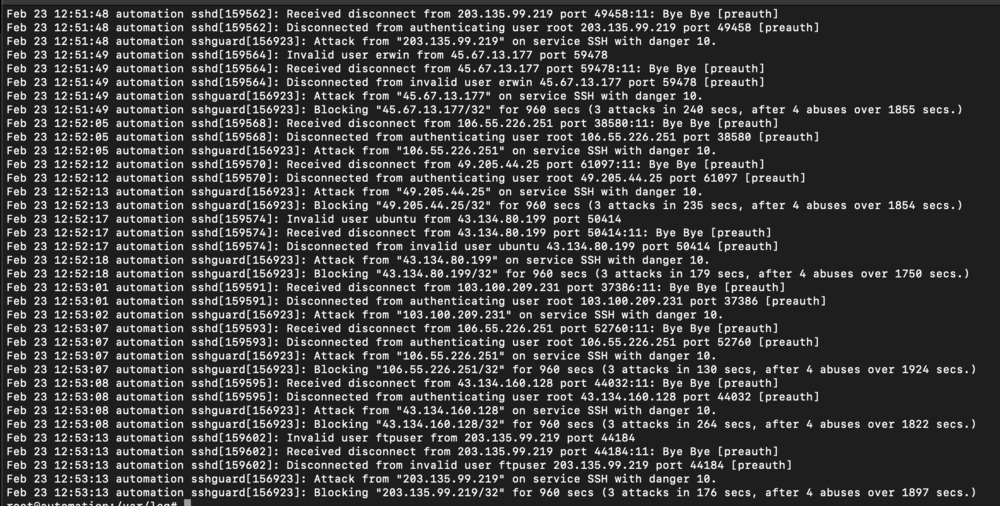
In conclusion, the steps taken to enhance the security of my servers have shown significant results. By generating and using SSH key pairs for authentication, disabling password-based login, and implementing SSHGuard to limit SSH connection attempts, I have effectively fortified my servers against unauthorized access and brute-force attacks. The examination of the SSH access logs post-security update reveals a considerable number of thwarted attempts and proactive blocking by SSHGuard, indicating the effectiveness of these measures. This proactive approach to server security has not only mitigated potential threats but also underscored the importance of continuous monitoring and updating security protocols to safeguard digital assets.

